Lab 1: How to Identify Threats & Vulnerabilities in an IT Infrastructure
Learning Objectives and Outcomes: Threats & Vulnerabilities Paper
Permalink:
Upon completing this lab, students will be able to:
- Identify common risks, threats, and vulnerabilities found throughout the seven domains of atypical IT infrastructure
- Align risks, threats, and vulnerabilities to one of the seven domains of a typical IT infrastructure
- Given a scenario, prioritize risks, threats, and vulnerabilities based on their risk impact to theorganization from a risk assessment perspective
- Prioritize the identified critical, major, and minor risks, threats, and software vulnerabilities foundthroughout the seven domains of a typical IT infrastructureRequired Setup and Tools
This is a paper-based lab and does not require the use of the ISS “mock” IT infrastructure or virtualized server farm.
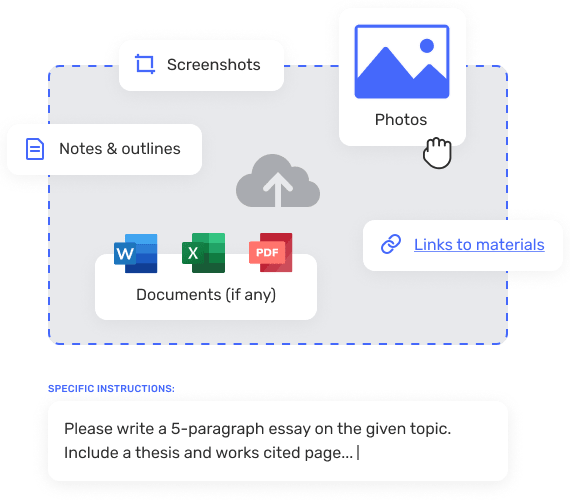
The standard Instructor and Student VM workstation with Microsoft Office 2007 or higher is required for this lab. Students will need access to Lab #1 – Assessment Worksheet Part A (a list of 21 risks, threats, and vulnerabilities commonly found in an IT infrastructure) and must identify which of the seven domains of a typical IT infrastructure the risk, threat, or vulnerability impacts.
In addition, Microsoft Word is a required tool for the student to craft an executive summary for management summarizing the findings and alignment of the identified risks, threats, and vulnerabilities that were found.
Recommended Procedures Lab #1 – Student Steps:
Student steps needed to perform Lab #1 – Identify Threats and Vulnerabilities in an IT Infrastructure:
- Connect your removable hard drive or USB hard drive to a classroom workstation.
- Boot up your classroom workstation and DHCP for an IP host address.
- Login to your classroom workstation and enable Microsoft Word.
- Review Figure 1 – Seven Domains of a Typical IT Infrastructure.
Copyright © 2013 Jones & Bartlett Learning, LLC, an Ascend Learning Company
www.jblearning.com
All Rights Reserved.
-3-
Current Version Date: 05/30/2011
Student Lab Manual
- Discuss how risk can impact each of the seven domains of a typical IT infrastructure: User, Workstation, LAN, LAN-to-WAN, WAN, Remote Access, Systems/Applications Domains.
- Work on Lab #1 – Assessment Worksheet Part A. Part A is a matching exercise that requires the students to align the risk, threat, or vulnerability with one of the seven domains of a typical IT infrastructure where there is a risk impact or risk factor to consider. Students may work in small groups of two or three.
- Have the students perform Lab #1 – Assessment Worksheet
- Answer Lab #1 – Assessment Questions and submit.Figure 1 – Seven Domains of a Typical IT Infrastructure
Deliverables
Upon completion of Lab #1 – Identify Threats and Vulnerabilities in an IT Infrastructure, students are required to provide the following deliverables as part of this lab:
- Lab #1 – Assessment Worksheet Part A. Identification and mapping of 21 risks, threats, and vulnerabilities to the seven domains of a typical IT infrastructure
- Lab #1 – Assessment Questions and Answers
Copyright © 2013 Jones & Bartlett Learning, LLC, an Ascend Learning Company
www.jblearning.com
All Rights Reserved.
-4-
Current Version Date: 05/30/2011
Student Lab Manual
Evaluation Criteria and Rubrics
The following are the evaluation criteria and rubrics for Lab #1 that the students must perform:
- Was the student able to identify common risks, threats, and vulnerabilities found throughout theseven domains of a typical IT infrastructure? – [ 25%]
- Was the student able to align risks, threats, and vulnerabilities to one of the seven domains of atypical IT infrastructure accurately? – [ 25%]
- Given a scenario in Part A, was the student able to prioritize risks, threats, and vulnerabilitiesbased on their risk impact to the organization? – [ 25%]
- Was the student able to prioritize the identified critical, major, and minor risks, threats, andsoftware vulnerabilities? – [ 25%]
Copyright © 2013 Jones & Bartlett Learning, LLC, an Ascend Learning Company Current Version Date: 05/30/2011
www.jblearning.com
All Rights Reserved.
-5-
Student Lab Manual
Lab #1: Assessment Worksheet
Part A – List of Risks, Threats, and Vulnerabilities Commonly Found in an IT Infrastructure
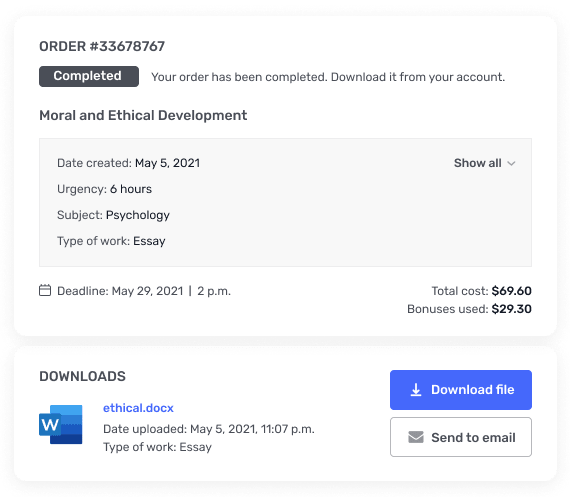
Course Name: _____________________________________________________________ Student Name: _____________________________________________________________ Instructor Name: ___________________________________________________________ Lab Due Date: _____________________________________________________________
Overview
The following risks, threats, and vulnerabilities were found in a healthcare IT infrastructure servicing patients with life-threatening situations. Given the list, select which of the seven domains of a typical IT infrastructure is primarily impacted by the risk, threat, or vulnerability.
Risk – Threat – Vulnerability
Unauthorized access from public Internet
User destroys data in application and deletes all files
Hacker penetrates your IT infrastructure and gains access to your internal network
Intra-office employee romance gone bad
Fire destroys primary data center
Communication circuit outages
Workstation OS has a known software vulnerability Unauthorized access to organization owned Workstations
Loss of production data
Denial of service attack on organization e-mail Server
Primary Domain Impacted
Copyright © 2013 Jones & Bartlett Learning, LLC, an Ascend Learning Company Current Version Date: 05/30/2011
www.jblearning.com
All Rights Reserved.
-6-
Student Lab Manual
Risk – Threat – Vulnerability
Remote communications from home office
LAN server OS has a known software vulnerability
User downloads an unknown e –mail attachment
Workstation browser has software vulnerability Service provider has a major network outage
Weak ingress/egress traffic filtering degrades Performance
User inserts CDs and USB hard drives
with personal photos, music, and videos on organization owned computers
VPN tunneling between remote computer and ingress/egress router
WLAN access points are needed for LAN connectivity within a warehouse
Need to prevent rogue users from unauthorized WLAN access
Primary Domain Impacted
Copyright © 2013 Jones & Bartlett Learning, LLC, an Ascend Learning